Introduction to Cybersecurity
Importance of Cybersecurity
Types of Cyber Threats
Malware
Phishing
Ransomware
Denial-of-Service Attacks
Man-in-the-Middle Attacks
Key Cybersecurity Practices
Strong Passwords
Multi-Factor Authentication
Regular Updates
Network Security
Data Encryption
Cybersecurity for Individuals
Cybersecurity for Businesses
Cybersecurity Tools
Antivirus Software
Firewalls
Intrusion Detection Systems
Security Information and Event Management (SIEM)
Legal and Regulatory Compliance
Cybersecurity Incident Response
Emerging Trends in Cybersecurity
Conclusion
1. Introduction to Cybersecurity
Cybersecurity is the practice of protecting systems, networks, and data from digital attacks. It involves using technologies, processes, and policies to prevent unauthorized access, disruption, or damage. The goal is to ensure confidentiality, integrity, and availability of information.
2. Importance of Cybersecurity
Cybersecurity is important to protect personal information, business data, and critical infrastructure. Attacks can cause financial loss, data breaches, and operational disruption. Implementing security measures reduces the risk of cyber incidents and ensures trust in digital operations.
3. Types of Cyber Threats
Malware
Malware is software designed to damage or gain unauthorized access to systems. Common types include viruses, worms, trojans, and spyware.
Phishing
Phishing uses fraudulent messages to trick individuals into revealing sensitive information such as login credentials or financial data.
Ransomware
Ransomware encrypts files on a system and demands payment to restore access. It can disrupt business operations and cause data loss.
Denial-of-Service Attacks
Denial-of-Service (DoS) attacks overload a system with traffic, making it unavailable to users. Distributed DoS (DDoS) uses multiple systems to amplify the attack.
Man-in-the-Middle Attacks
Man-in-the-Middle (MITM) attacks intercept communication between two parties to steal or manipulate data.
4. Key Cybersecurity Practices
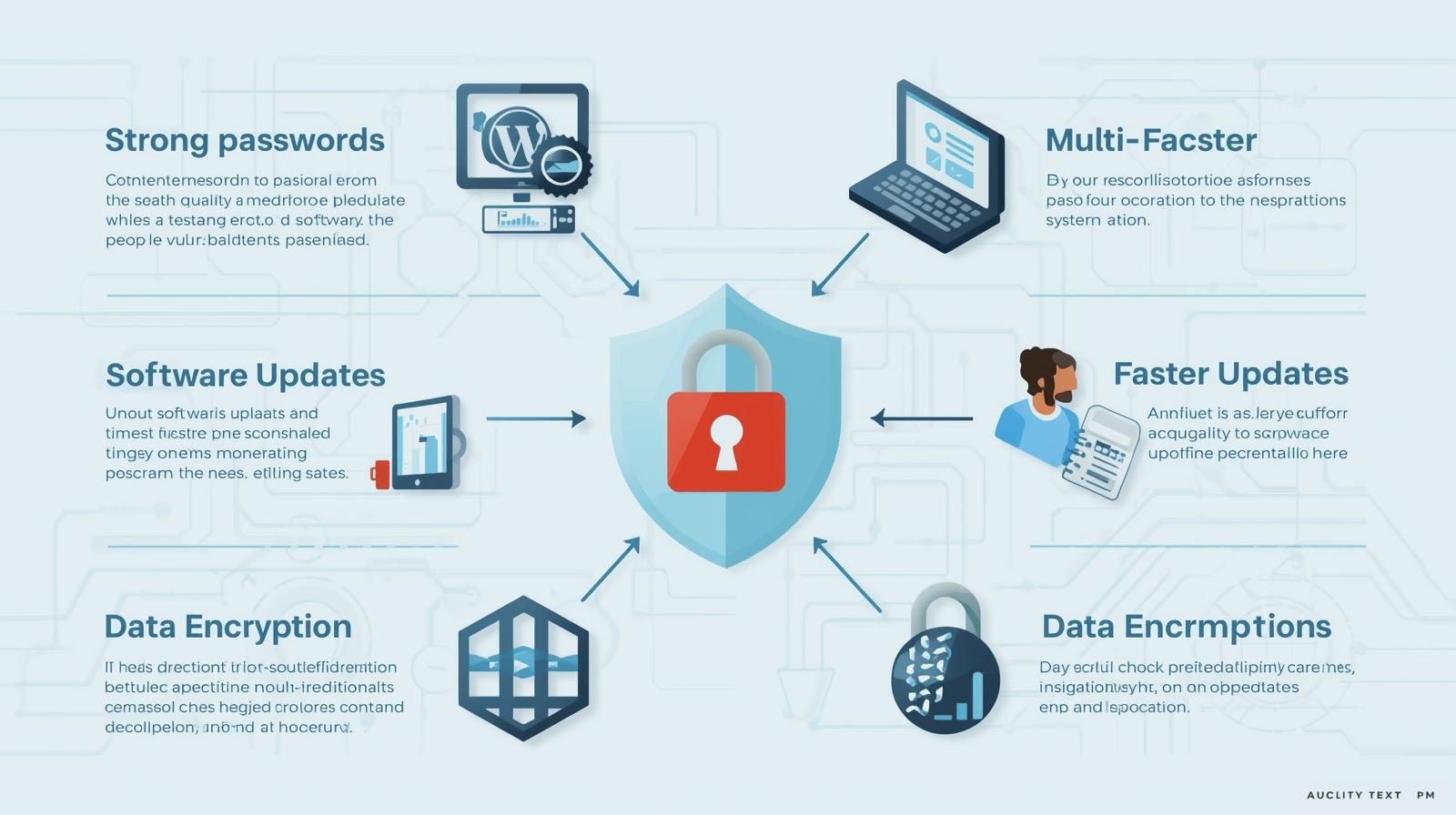
Strong Passwords
Using complex and unique passwords for each account reduces the risk of unauthorized access.
Multi-Factor Authentication
Adding multiple verification steps, such as OTP or biometric verification, strengthens account security.
Regular Updates
Installing updates and patches for software and operating systems fixes vulnerabilities that attackers can exploit.
Network Security
Securing networks with firewalls, VPNs, and intrusion detection systems prevents unauthorized access and monitoring.
Data Encryption
Encrypting sensitive data ensures that even if it is intercepted, it cannot be read without the encryption key.
5. Cybersecurity for Individuals
Individuals should protect personal devices, use strong passwords, avoid suspicious links, and back up data regularly. Awareness of common threats is key to staying secure.
6. Cybersecurity for Businesses
Businesses should implement comprehensive security policies, employee training, secure networks, and incident response plans. Protecting customer data and critical systems is essential to maintaining operations and trust.
7. Cybersecurity Tools
Antivirus Software
Antivirus software scans and removes malware from devices to prevent infection.
Firewalls
Firewalls monitor and control incoming and outgoing network traffic to block unauthorized access.
Intrusion Detection Systems
IDS detects and alerts on suspicious activities on the network, helping to respond to attacks quickly.
Security Information and Event Management (SIEM)
SIEM tools collect and analyze security data, providing real-time insights into threats and breaches.
8. Legal and Regulatory Compliance
Regulations such as GDPR, HIPAA, and CCPA require organizations to follow cybersecurity standards. Compliance ensures data protection and avoids legal penalties.
9. Cybersecurity Incident Response
Incident response involves identifying, analyzing, and mitigating security incidents. Organizations should have predefined plans to minimize impact and recover quickly.
10. Emerging Trends in Cybersecurity
Trends include AI-based threat detection, zero-trust architecture, cloud security, and IoT security. Organizations must adapt to evolving threats to maintain protection.